![PDF] Implementing AES Encryption on Programmable Switches via Scrambled Lookup Tables | Semantic Scholar PDF] Implementing AES Encryption on Programmable Switches via Scrambled Lookup Tables | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e81407dd221afd6c1533ef2e688e83c096c1a78f/3-Figure1-1.png)
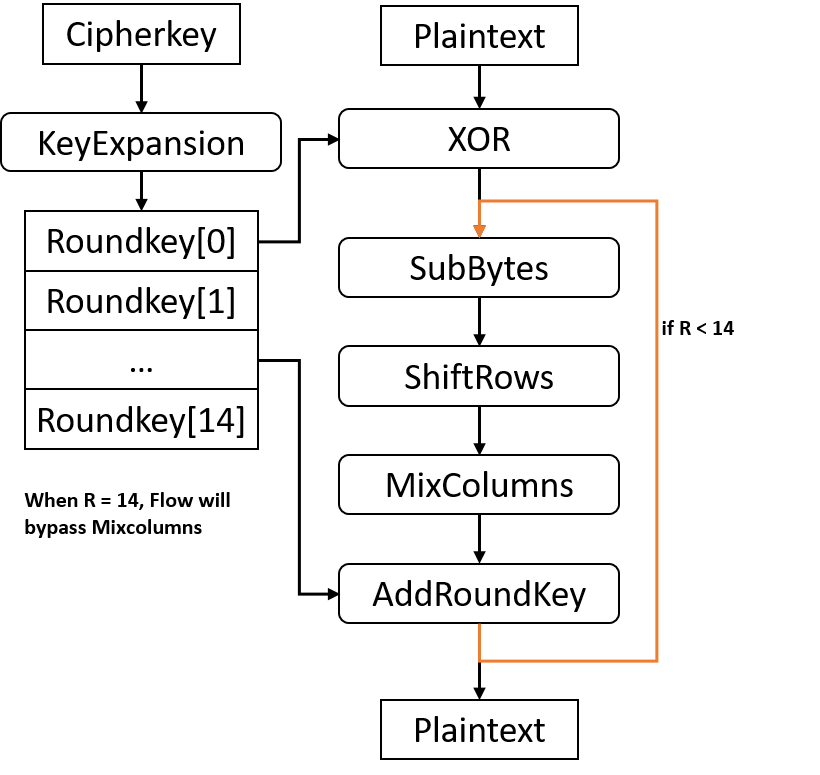
PDF] Implementing AES Encryption on Programmable Switches via Scrambled Lookup Tables | Semantic Scholar
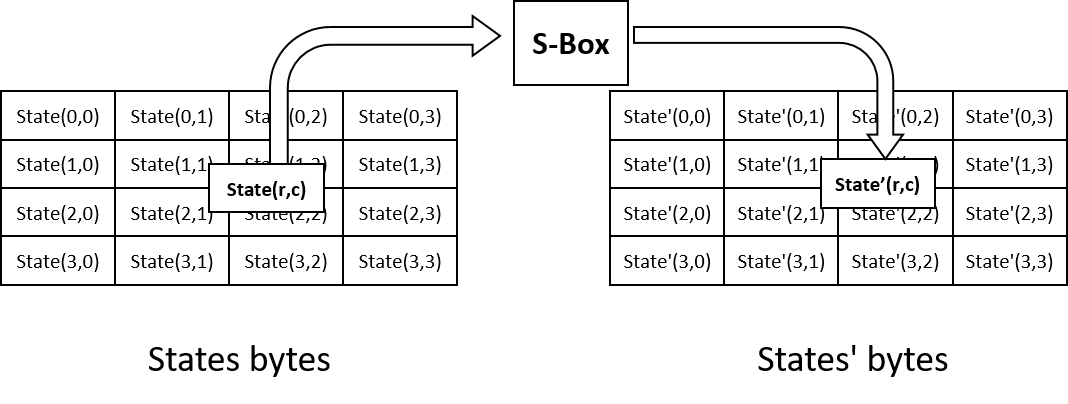
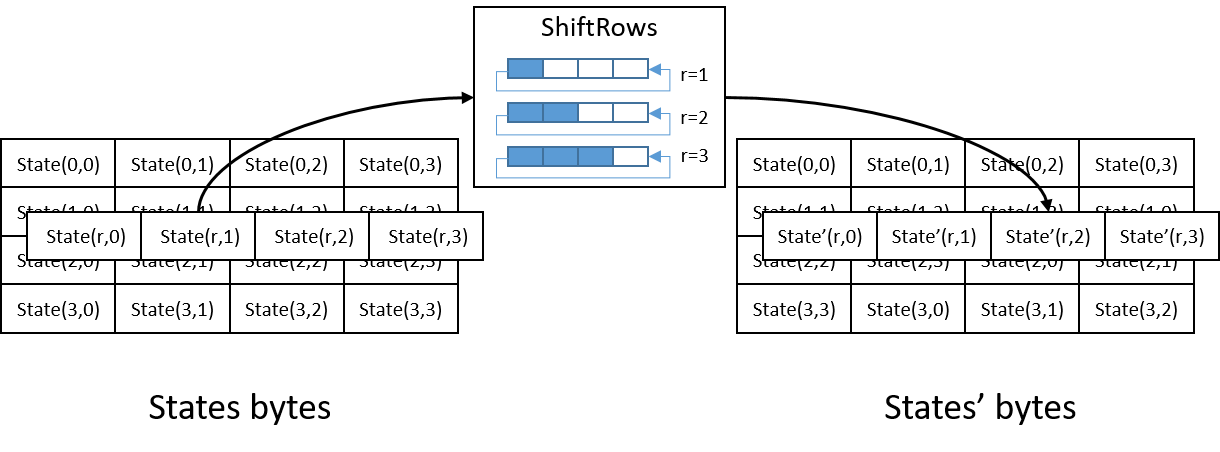
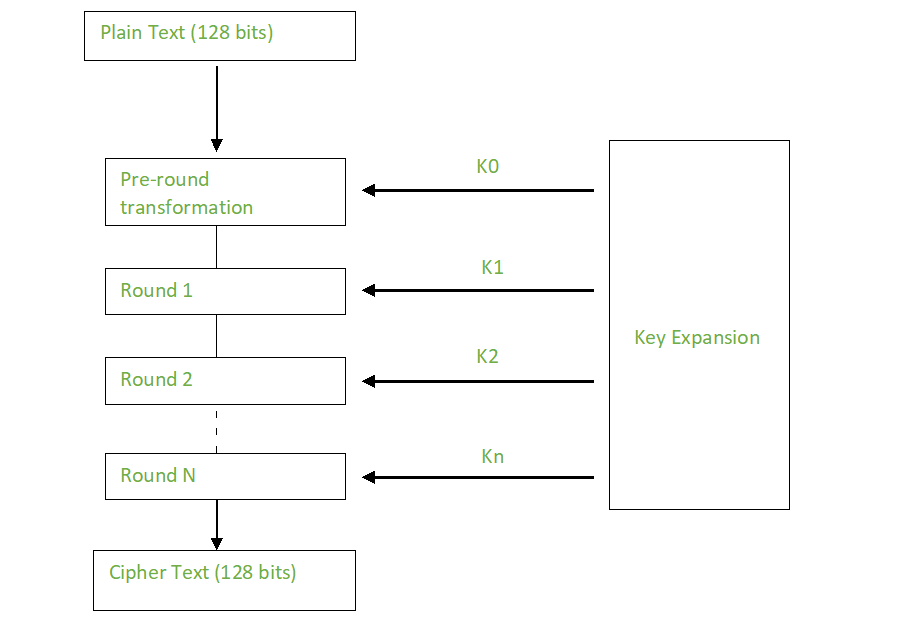
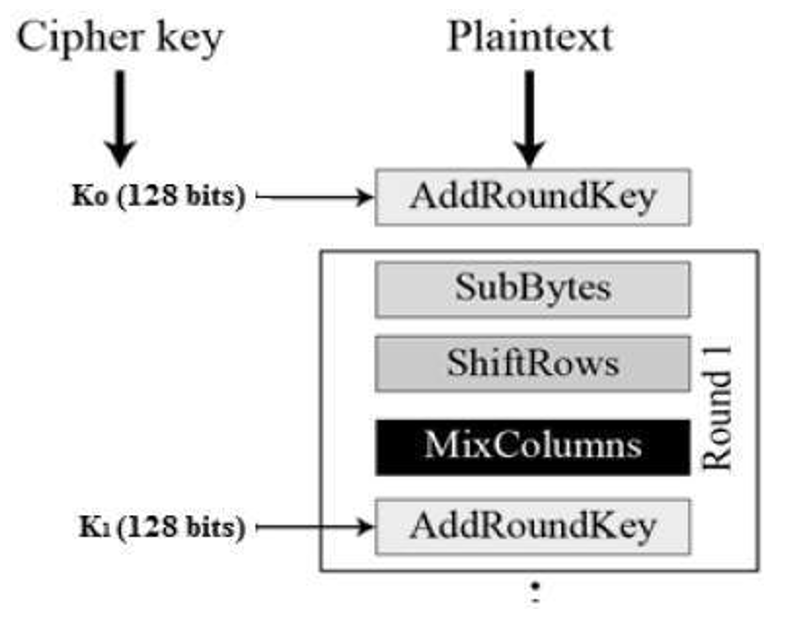
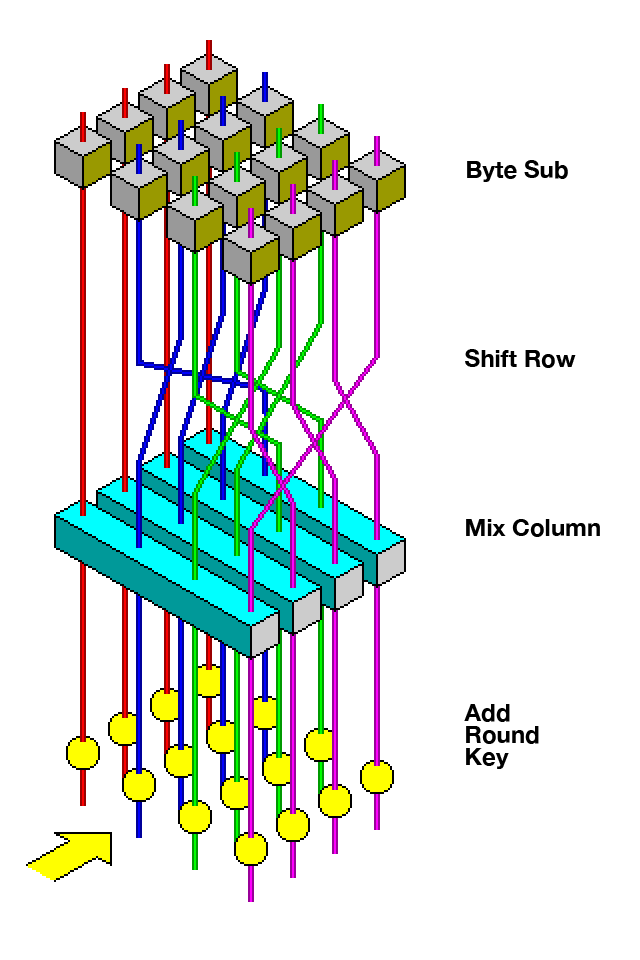
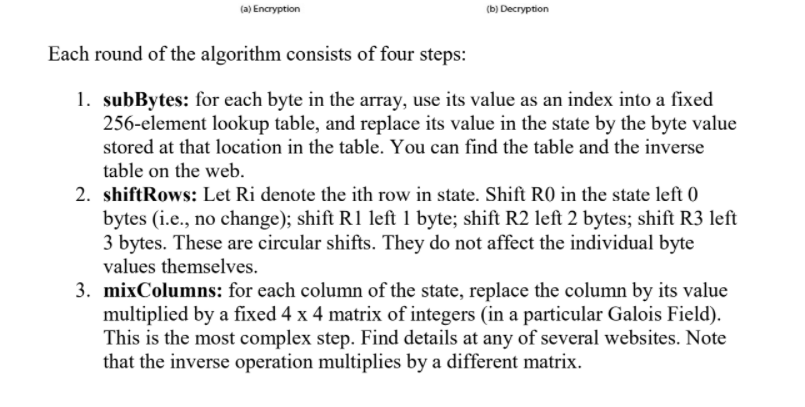
Steps in the AES Encryption Process :: Appendix A. Overview of the AES Block Cipher :: Appendixes :: 802.11 security. wi-fi protected access and 802.11i :: Networking :: eTutorials.org
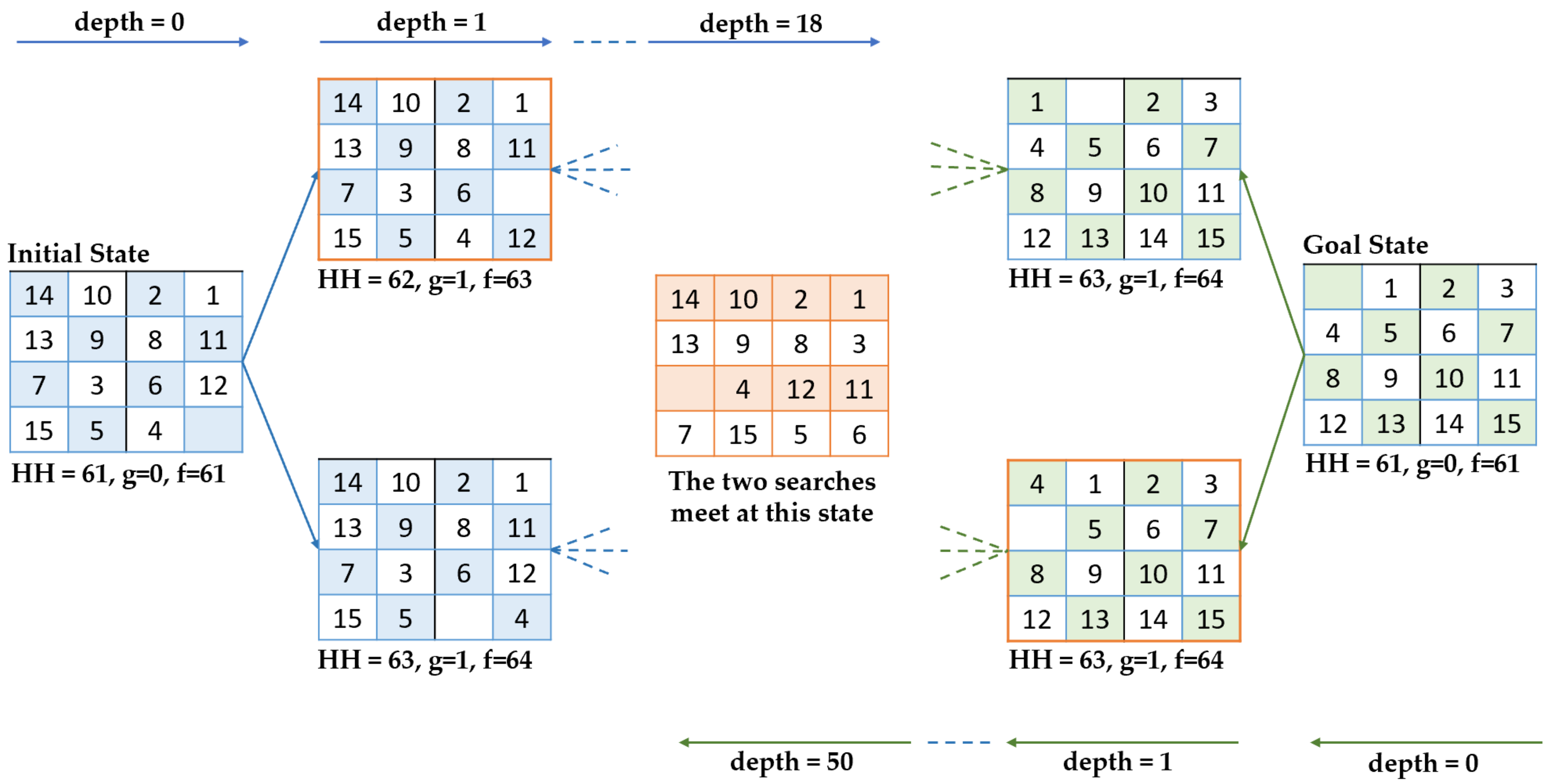
Computers | Free Full-Text | The Fifteen Puzzle—A New Approach through Hybridizing Three Heuristics Methods

![PDF] High-level simulation for side channel attacks | Semantic Scholar PDF] High-level simulation for side channel attacks | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/f3a5ceffa907e5b328900d0891d38acc867db710/2-Table1-1.png)


![3: AES: SubBytes() function (taken from [8]) | Download Scientific Diagram 3: AES: SubBytes() function (taken from [8]) | Download Scientific Diagram](https://www.researchgate.net/publication/265112905/figure/fig3/AS:644285556858931@1530621055885/AES-SubBytes-function-taken-from-8.png)